A combination of several different approaches using a variety of malware elements generating multiple forms of viruses worms and trojan horses.
Explain different security threats.
The most common network security threats 1.
Virtually every cyber threat falls into one of these three modes.
We ve all heard about them and we all have our fears.
Disgruntled employees internal attacks are one of the biggest threats facing your data and systems states cortney thompson cto of green house data.
Arm yourself with information and resources to safeguard against complex and growing computer security threats and stay safe online.
Perform regular threat assessments to determine the best approaches to protecting a system against a specific threat along with assessing different types of threats.
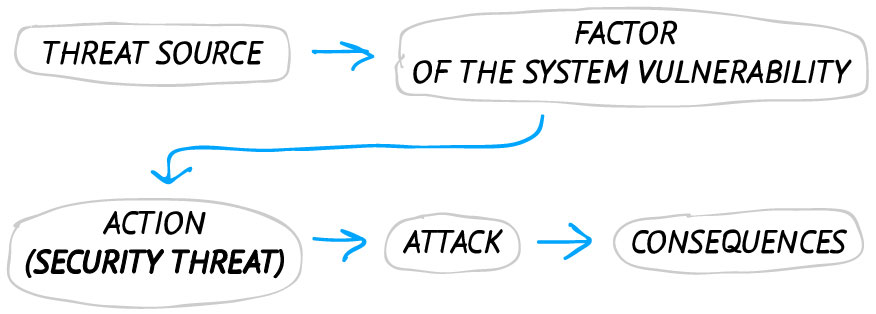
Security threat short description.
Conduct penetration testing by modeling real world threats in order to discover vulnerabilities.
The security policy not only defines security roles but also how to respond to specific physical and virtual threats.
Masters of disguise and manipulation these threats constantly evolve to find new ways to annoy steal and harm.
Attackers are after financial gain or disruption espionage including corporate espionage the theft of patents or state espionage.
Types of cybersecurity threats.
Although the terms security threat security event and security incident are related in the world of cybersecurity these information security threats have different meanings.
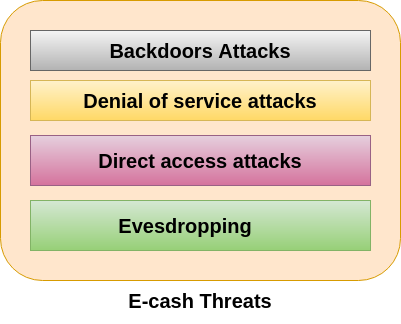
In information security threats can be many like software attacks theft of intellectual property identity theft theft of equipment or information sabotage and information extortion.
Computer security threats are relentlessly inventive.
Different types of computer system security threat there are many different types of security threats to computer systems as follows.
Cybersecurity threats come in three broad categories of intent.
We ve covered the history of web exploiting and the biggest exploits the world has experienced but today we re going back to basics exploring and explaining the most common network security threats you may encounter while online.